Introduction
Following up on my Google’s Cybersecurity Professional Certificate quest, I’ll share the cliff notes of the courses as I go through them. Dense summaries of what actually matters.
Today: Sound the Alarm: Detection and Response
From alert to recovery
Security operations center around a four-phase cycle (from the NIST Incident Response Lifecycle):
- Preparation
- Detection and Analysis
- Containment/Eradication/Recovery
- Post-Incident Activity
This framework aligns with the NIST Cybersecurity Framework’s core functions of Detect, Respond, and Recover.
Couple of key points from module 1.
- Events versus Incidents: An event is any observable network occurrence (like a password reset), while an incident specifically violates security policies or threatens confidentiality, integrity, or availability
- The Five W’s guide every investigation: Who triggered it, What happened, When it occurred, Where it took place, and Why it happened
- Documentation starts immediately through tools like the Incident Handler’s Journal and Chain of Custody logs, which track evidence possession from collection to legal proceedings
CSIRT and SOC
Modern security requires specialized roles working in concert. Computer Security Incident Response Teams (CSIRT) focus on incident management, while Security Operations Centers (SOCs) handle continuous monitoring.
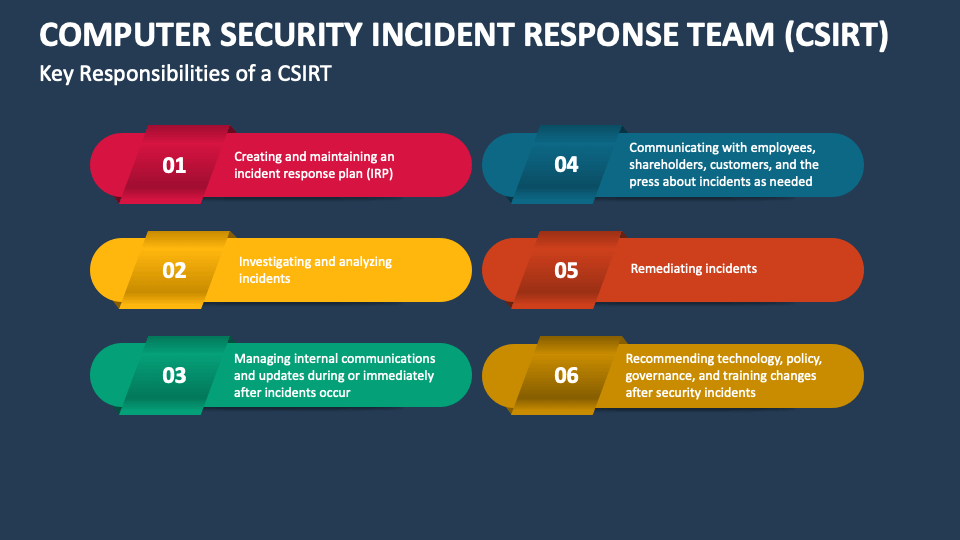
- CSIRT key roles include Security Analysts (investigate and triage), Technical Leads (guide containment strategies), and Incident Coordinators (ensure communication flow)
- SOC tiers create escalation paths
- Tier 1 analysts monitor and prioritize alerts
- Tier 2 conducts deeper investigations
- Tier 3 leads perform advanced forensics
- SOC Managers handle strategy and communication
- Supporting functions include Threat Hunters (proactively seek advanced threats), Forensic Investigators (preserve digital evidence), and coordination with Legal and PR teams during breaches
Network traffic and monitoring
Network traffic analysis relies on baselines of normal behavior to identify Indicators of Compromise (IoC). Unusual patterns, like large outbound transfers during off-hours, often signal data exfiltration.
- Attack patterns typically follow
- Initial access (phishing)
- Lateral movement/pivoting
- Asset identification
- Data compression
- Data exfiltration
- Key monitoring targets include flow analysis (unusual port/protocol combinations), payload inspection (sensitive data leaving networks), and temporal patterns (activity outside business hours)
tcpdumpserves as the foundational command-line capture tool, using syntax likesudo tcpdump -i any -nto capture all interfaces without DNS resolution (preventing attacker notification)
Data breaks into discrete units containing three components:
- Header. Routing information including source/destination IPs, ports, and protocol (TCP/UDP)
- Payload. The actual transmitted data
- Footer. Signifies packet termination
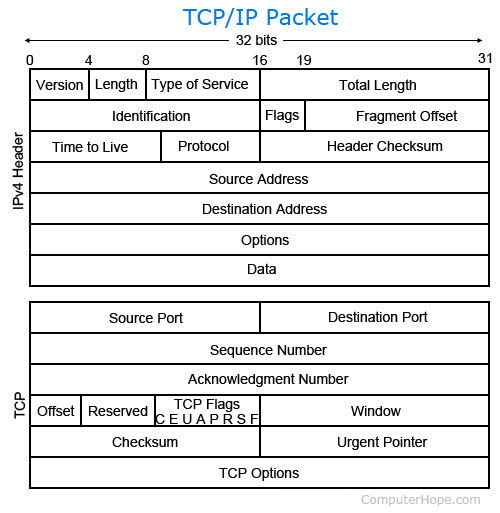
IPv4 headers contain Version, IHL, ToS, Total Length, TTL (prevents infinite loops), and checksum fields; IPv6 simplifies this to eight fields including Traffic Class and Hop Limit.
Detection technologies
Intrusion Detection Systems (IDS) tools monitor activity through two deployment strategies:
- Host-based IDS (HIDS). Endpoint agents monitoring file systems, resource usage, and user actions on individual machines
- Network-based IDS (NIDS). Strategic network placement watching traffic flows across multiple systems for lateral movement detection
Two analysis methods power these tools:
- Signature-based. Matches activity against known malicious patterns (low false positives but blind to zero-days)
- Anomaly-based. Flags deviations from behavioral baselines (catches unknown threats but higher false positive rates)
Log tooling
Security teams must interpret diverse log structures without universal standards.
- JSON. Lightweight key-value pairs and arrays, common in cloud environments
- Syslog. Unix standard with Header (timestamp/hostname), structured data (key-values), and message components
- XML. Windows native format using tagged elements and attributes
- Common Event Format (CEF). Pipe-separated structure designed for security tools
Critical practice: Tailor logging to specific needs rather than capturing everything, balancing investigation value against performance costs and PII restrictions.
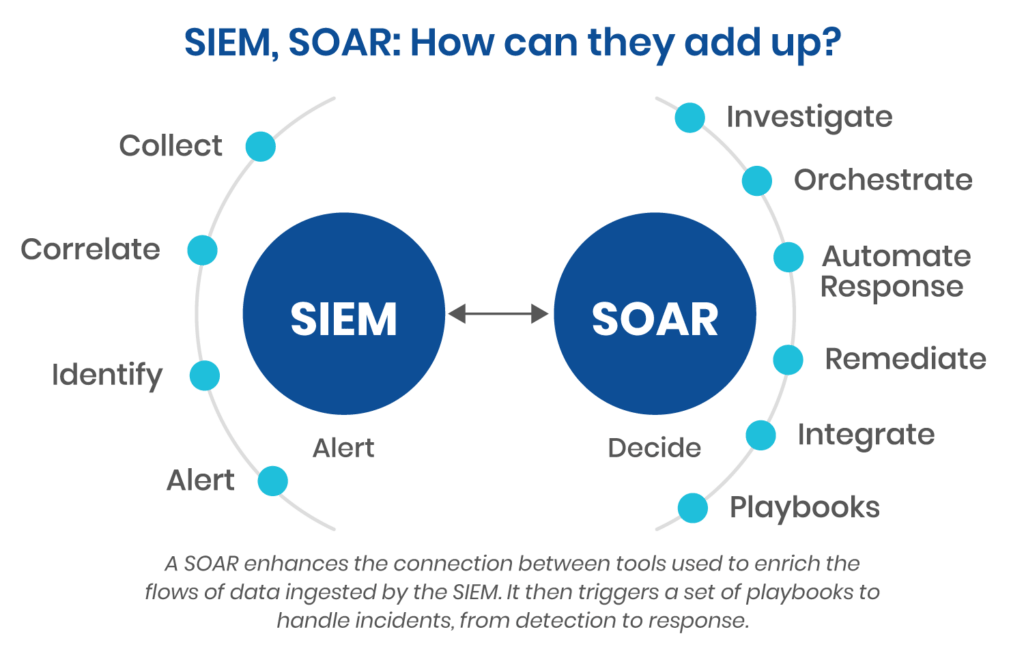
Security Information and Event Management (SIEM) tools follow a three-step process:
- Collect and aggregate data from firewalls, servers, and endpoints
- Normalize data into standard formats for cross-source searching
- Analyze against rules to generate alerts
- Log forwarders automate data ingestion from distributed sources
Key distinction: SIEM collects, analyzes, and reports for human review, while Security Orchestration, Automation, and Response (SOAR) automates analysis and response workflows, tracking multiple incidents as centralized cases.
Investigation and response workflow
The detection and analysis phase faces inherent challenges: impossible to catch everything, resource constraints on automated tools, and alert volume fatigue (often from misconfigured rules).
- Triage follows hospital emergency protocols: Receive and assess alert validity, assign priority based on functional impact and recoverability, then collect evidence and analyze
- Threat Hunting adds proactive human-driven searches combining technology with intuition to uncover fileless malware and advanced persistent threats missed by automation
Investigations leverage two evidence types:
- Indicators of Compromise (IoC). Forensic artifacts identifying “who” and “what” after attacks (malicious filenames, IP addresses, file hashes)
- Indicators of Attack (IoA). Behavioral evidence showing “how” and “why” of ongoing incidents (processes making unusual network connections)
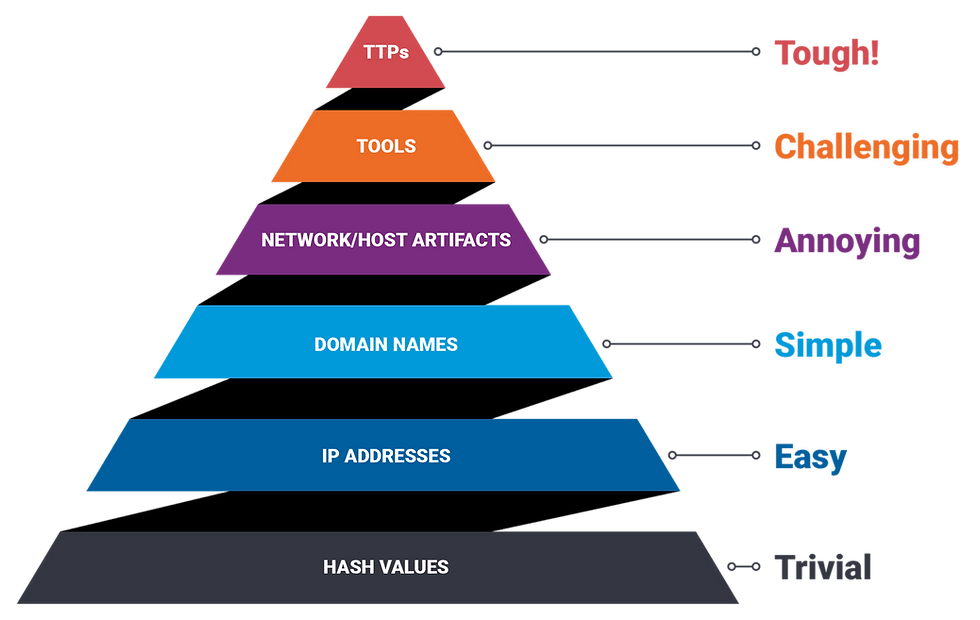
The Pyramid of Pain ranks IoCs by attacker disruption difficulty:
- Hash values (trivial to change)
- IP addresses and domains (easy to swap)
- Network and host artifacts (moderate difficulty)
- Tools (requires new software)
- Tactics, Techniques, and Procedures (TTPs): Maximum impact when blocked, as these behavioral patterns are hardest for attackers to modify
Tools like VirusTotal and Information Sharing and Analysis Centers (ISACs) provide crowdsourced threat intelligence, preventing attackers from reusing the same exploits across multiple organizations.
Response executes through three interrelated steps.
- Containment. Isolate affected systems to limit damage (disconnecting infected machines, blocking IPs at firewalls)
- Eradication. Remove threat elements through vulnerability patching and malware removal
- Recovery. Restore operations via system reimaging, password resets, and configuration hardening
Business Continuity Plans ensure resilience through hot sites (immediate failover), warm sites (quickly activated), and cold sites (infrastructure requiring setup)
Documentation
Effective incident response requires meticulous documentation for transparency, standardization, and clarity.
- Playbooks provide structured response procedures for specific attack types (ransomware, DDoS, data breaches), available as non-automated, automated, or semi-automated workflows
- Chain of Custody logs maintain evidence integrity for legal admissibility
- Post-Incident analysis. Lessons learned meetings held within two weeks identify process gaps and generate actionable improvements, closing the cyclical response loop
Modern security extends to CI/CD pipelines, monitoring for unauthorized code changes, suspicious deployment patterns, and compromised dependencies. Combining automated monitoring with threat intelligence creates rapid detection capabilities that limit supply chain damage.
Effective response ultimately balances precision tools (signature detection) with adaptive methods (anomaly detection), ensuring teams see their networks clearly and act decisively when seconds count.
Next
I think this one has been the biggest write up yet in the Google Cyber series. It was interesting material, still a bit heavy in the theory side.
Next course is the complete opposite, or so I assume, since it is all about Python.