Introduction
Last course of my Google’s Cybersecurity Professional Certificate adventure. I’ll cover everything except for the AI module. This one will deserve some special attention (next week).
As always, I’ll share the cliff notes on the courses as I go. Dense summaries of what actually matters.
Today: Put It to Work: Prepare for Cybersecurity Jobs.
Adopt a security mindset
A security mindset is nothing more than a habit of constantly asking two questions:
- What am I protecting?
- Who wants it?
- From a simple phishing email to a nation‑state ransomware campaign, every threat vector aims at the same thing: your most valuable assets
How the mindset translates into action:
- Daily risk‑check. Stay current on emerging threats and scrutinize every user action
- Prioritize by impact. Treat a compromised database of customer SSNs as a high‑level incident, but a forgotten website URL as low‑level
- Escalate early. Even a tiny alert could be the first domino of a larger breach
- Lifecycle thinking. Identify, assess, protect, and continuously monitor
Business continuity & disaster recovery are key. A solid Business Continuity Plan (BCP) maps out how the company stays alive during a disruption, while a Disaster Recovery Plan (DRP) spells out the steps to bring systems back after a security incident.
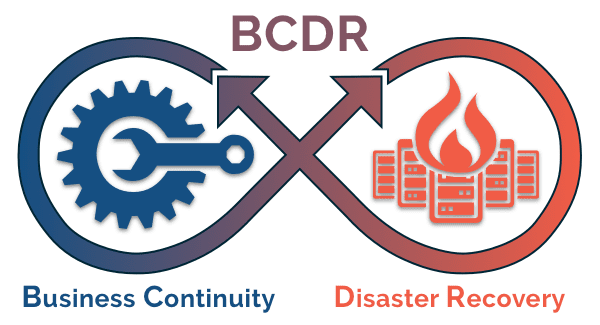
Both are written together, tested by cross‑functional teams, and kept up‑to‑date. Think of them as the emergency exits on a plane: you hope you never need them, but you’re grateful they exist.
Incident escalation
When a potential threat shows up, an analyst’s job is to:
- Detect. Notice the odd login spikes, an unapproved executable, or a suspicious email
- Triage. Evaluate severity, asset criticality, and whether the alert fits a known pattern
- Escalate. Hand it off to the right owner if it crosses the threshold
Roles in the escalation process:
| Role | What they care about |
|---|---|
| Data owner | Who may read/write the data |
| Data controller | Compliance with privacy laws |
| Data custodian | Access controls & technical safeguards |
| DPO | Regulatory adherence and breach notifications |
| CISO | Business impact, reputation, and legal exposure |
Types of incidents that always go up the chain:
- Malware infection. Ransomware, trojans, or any malicious code that could lock or corrupt data
- Unauthorized access. A brute‑force break‑in or an insider using credentials they shouldn’t
- Improper usage. Policy violations, even accidental ones, that could create gaps
Stakeholder communication
Security professionals are the translators between technical alerts and the executive board. The art lies in giving the right amount of information, to the right person, in the right format.
So who needs to hear what?
| Stakeholder | What they care about | Best channel |
|---|---|---|
| Risk managers | Overall risk exposure, compliance & reporting | Concise email + link to risk dashboard |
| Operations managers | Immediate impact on daily workflow & system uptime | IM or ticket alert (follow‑up email) |
| CFO | Financial consequences, cost of remediation | Email with concise summary + cost estimate |
| CEO | Overall risk posture, strategic implications | Slide deck or executive brief |
| CISO | Technical depth, compliance gaps | Detailed report + visual dashboard |
Crafting your security story, the below 4 elements should always be present.
- Conflict. “We’ve observed a spike in failed log‑ins on the finance portal.”
- Impact. “If left unchecked, this could lead to credential stuffing and a breach of financial data.”
- Playbook reference. “This aligns with the ‘Credential Abuse’ response procedure (Section 4).”
- Solution. “Temporarily enforce MFA and initiate a password reset for affected accounts.”
Communication etiquette:
- Keep jargon out of the CEO’s inbox
- Use approved channels (ticketing system, encrypted email)
- Follow up within the agreed SLA. No reply can be as damaging as a missed alarm

Resources and community
Cybersecurity never sleeps, so you need a feeding plan for both knowledge and network.
| Category | Where to go |
|---|---|
| Threat trends | OWASP Top 10, Krebs on Security, Dark Reading |
| Leadership insights | CSO Online, CISO LinkedIn feeds |
| Hands‑on learning | BSides talks, local incident‑response meet‑ups, free labs on GitHub |
| Professional groups | (ISC)² chapters, InfraGard, local ‘Incident Response’ LinkedIn groups |
Note: a lot of these live resources are for US specifically and right from the suggested resources from this Google course. I myself am not from the US, and therefore don’t have personal experience with these suggestions.
Building a career without a PhD:
- Follow a few CISO profiles. They often share what tools, frameworks, or certifications their teams value
- Connect with purpose. Send a short, error‑free note to cybersecurity professionals asking if they have tips, want to connect, etc.
- Leverage classmates. Study partners become interview buddies and referral sources
- Attend low‑cost events. Virtual BSides, local meet‑ups, or free webinars are goldmines for conversation starters
Continuous learning is the strongest signal you can send to any hiring manager. Keep a reading list, schedule weekly “security news hour,” and let your LinkedIn activity reflect the latest trends you’re mastering.
Next
This one was actually pretty cool, and I did not expect it. Some pretty useful stuff in there.
Next week will be the last in this series and it is all about AI. This opened up my eyes that I need to expand my interests, if I want to be successful in this space.
Looking forward to it!