Introduction
As previously said, I’m tackling Google’s Cybersecurity Professional Certificate and I’ll share the cliff notes as I go. Dense summaries of what actually matters.
Today: Play It Safe: Manage Security Risks
Security domains and risk management
Security teams organize their work across eight critical domains, ranging from governance (Security and Risk Management) to hands-on technical areas like Network Security, Identity and Access Management (IAM), and Software Development Security. At the center of this structure lies your security posture: your organization’s ability to defend critical assets and react to change.
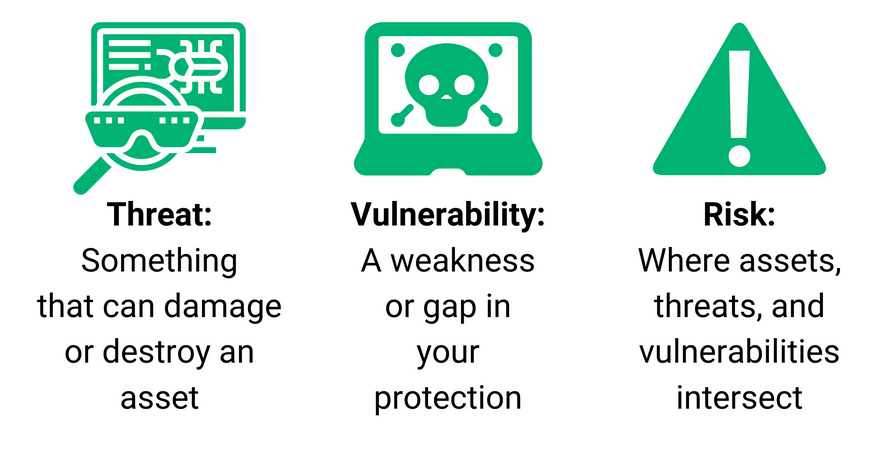
Understanding the risk landscape starts with three key terms:
- Threat. A circumstance that can negatively impact assets (e.g., social engineering)
- Vulnerability. A weakness that can be exploited (e.g., outdated firewalls, weak passwords)
- Risk. The likelihood of a threat exploiting a vulnerability, impacting confidentiality, integrity, or availability
The NIST Risk Management Framework (RMF) provides a seven-step cycle to manage this:
- Prepare
- Categorize
- Select
- Implement
- Assess
- Authorize
- Monitor
This structured approach ensures security is proactive rather than reactive.
Frameworks, controls and audits
Security frameworks are the blueprints for mitigating risks like social engineering and ransomware. They provide standardized guidelines to protect data and privacy, with particular attention to the human element, which is still the biggest variable in any security equation.
Security controls serve as the actual safeguards:
- Encryption (converting plaintext to ciphertext)
- Authentication (verifying identity)
- Authorization (granting permissions)
These are governed by standards such as the NIST Cybersecurity Framework (CSF), which outlines six operational functions:
- Govern
- Identify
- Protect
- Detect
- Respond
- Recover
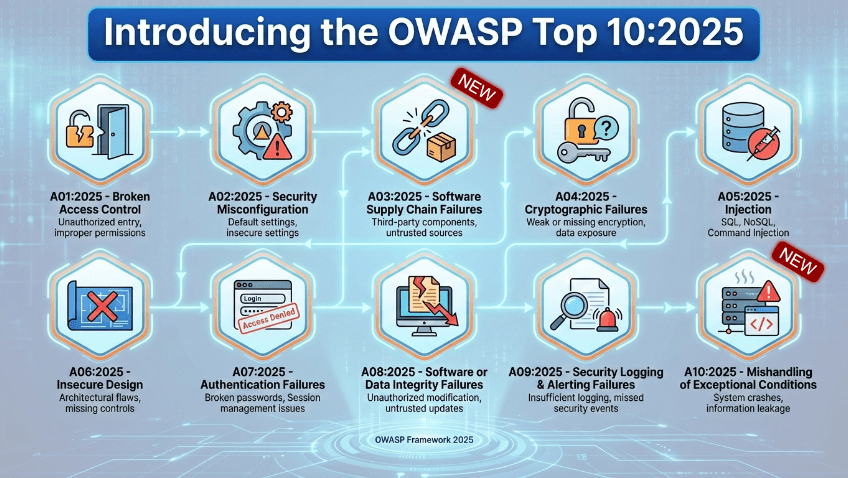
For application security, OWASP principles emphasize defense in depth, failing securely (defaulting to the safest option when systems error), and avoiding “security by obscurity.”
Other key standards include the Cyber Threat Framework (CTF), providing common language for government and private sector threat communication, and ISO/IEC 27001, which enables organizations of all sizes to manage financial data, intellectual property, and third-party information.
Internal security audits verify that these frameworks work in practice. Effective audits establish scope and goals, conduct risk assessments to identify potential threats, and evaluate controls across three categories:
- Administrative
- Technical
- Physical
They assess compliance with regulations like GDPR (critical for payment processors), rank risks by urgency, and communicate actionable recommendations to stakeholders.
Monitoring and SIEM evolution
You can’t protect what you can’t see. Logs (firewall, network, server) record system events, but Security Information and Event Management (SIEM) tools transform this data into intelligence.
Modern SIEM provides real-time visibility, automated alerts, and customizable dashboards that track metrics like response times and failure rates. The market is shifting rapidly toward cloud native solutions that offer scalability and AI integration, while traditional platforms like Splunk dominate the self hosted enterprise space.
Key trends driving change:
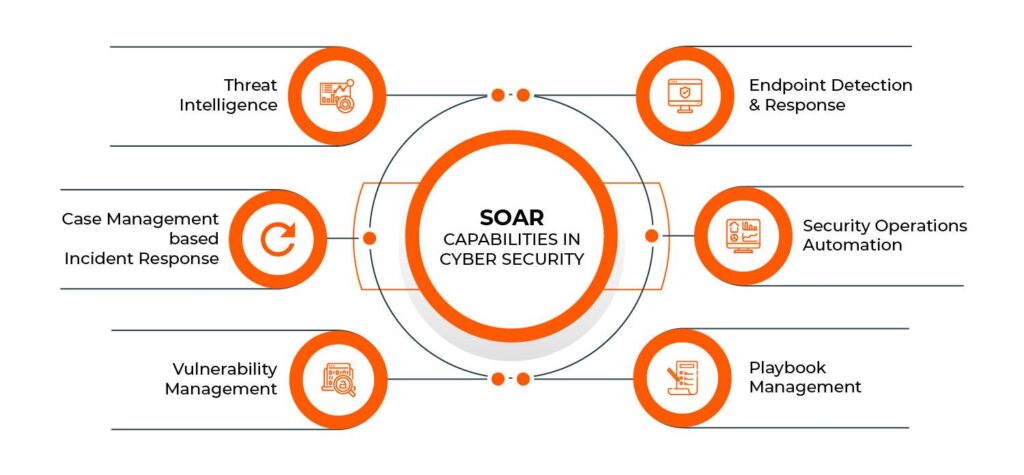
- Security Orchestration, Automation and Response (SOAR) integration to automate routine incident handling
- Artificial Intelligence/Machine Learning (AI/ML) for threat detection and pattern recognition
- Cloud hosted models replacing legacy infrastructure
Incident handling and playbooks
When prevention fails, incident response (IR) determines the damage. Effective IR follows six phases:
- Preparation
- Detection & Analysis
- Containment
- Eradication & Recovery
- Post-Incident Activity
- Coordination
Speed and accuracy are critical. Playbooks (or runbooks) provide step-by-step guides for specific scenarios, ensuring consistent responses. When combined with SOAR tools, organizations can automate repetitive tasks (like auto-blocking accounts after multiple failed logins) while analysts focus on complex investigation and root cause analysis.
Modern security is a continuous cycle: establish domains and frameworks, monitor with intelligent tools, and respond with automated precision.
Next
This was quite a lot, and not the most exciting material. We needed to cover it though. Next up are networks and network security, which is something completely different and a bit more fun.