Introduction
As part of tackling the Google’s Cybersecurity Professional Certificate, I’ll share the cliff notes on the courses as I go. Dense summaries of what actually matters.
Today: Connect and Protect: Networks and Network Security
Traffic and architecture
An entry level analyst parses logs and analyzes traffic across network layers. Physical infrastructure includes firewalls (first defense), routers (Layer 3/IP direction), and switches (Layer 2/MAC forwarding). Modern environments use Software Defined Networking (SDN), where these devices become virtual services hosted by cloud providers, offering pay-as-you-use scalability and rapid security deployment.
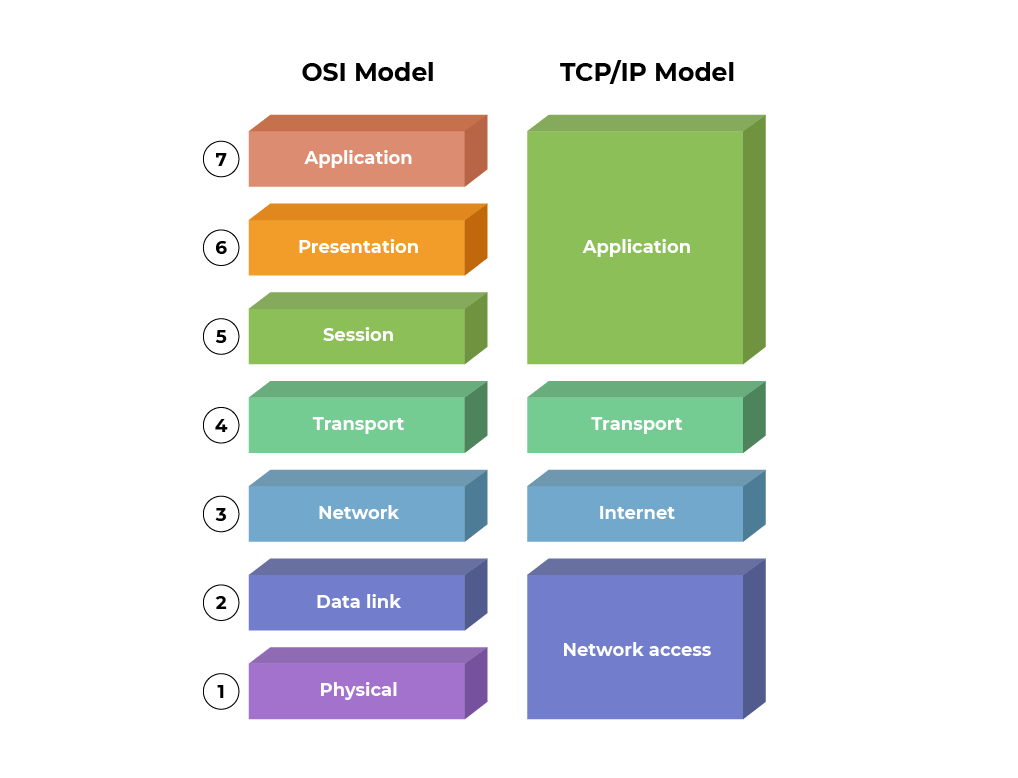
Data travels in packets containing headers (source/destination IPs, MAC addresses, protocols), bodies (payloads), and footers (end signals). The TCP/IP model organizes transmission across four layers:
- Network Access. Hardware, cables, and ARP mapping
- Internet. IP routing between networks and ICMP error reporting
- Transport. TCP (reliable, connection-oriented) versus UDP (fast, connectionless)
- Application. HTTP, SMTP, DNS, and other user-facing protocols
The OSI model expands this to seven layers, adding Presentation (encryption) and Session (connection management), and splitting the network access layer into Physical (hardware) and Data Link (local transmission). IPv4 provides 4.3 billion addresses with complex headers, while IPv6 offers vastly more addresses with simplified headers and improved security management.
Protocols and perimeters
Network protocols govern device communication:
- TCP establishes verified connections via handshake
- ARP resolves MAC addresses for next-hop delivery
- HTTPS encrypts traffic via SSL/TLS
- DNS translates domains to IPs
Firewalls range from stateless (static rules only) to stateful (tracking connection behavior) to next-generation (NGFW) with deep packet inspection and cloud threat intelligence. VPNs create secure tunnels via WireGuard (modern, fast) or IPSec (established, complex), while SD-WAN connects distributed offices securely.
Security zones segment risk:
- Uncontrolled zone (internet)
- Controlled zone (protected subnets)
- DMZ (public-facing services between internet and internal network)
- Restricted zone (sensitive data behind additional firewalls)
Subnetting via CIDR notation (e.g., /24) creates these isolated neighborhoods efficiently.
The threat landscape
Attackers intercept traffic through packet sniffing (passive reading or active manipulation) to steal credentials or alter data. Defense requires avoiding open wifi, using HTTPS, and deploying VPNs.
Denial of Service attacks overwhelm systems through:
- SYN floods. Exploiting TCP handshakes by sending connection requests without completion, exhausting ports
- ICMP floods. Bandwidth exhaustion via continuous ping responses
- Ping of Death. Single oversized packets crashing vulnerable systems
IP spoofing changes packet source addresses to bypass filters, enabling on-path attacks (intercepting and altering communications between trusted devices), replay attacks (retransmitting captured packets to impersonate users), and smurf attacks (broadcasting spoofed packets to amplify responses).
Defense in Depth
Security hardening reduces attack surface through immediate patching (attackers exploit known flaws rapidly), disabling unused ports and services, establishing baseline configurations for anomaly detection, and enforcing multi factor authentication (something known, something possessed, and something you are, a.k.a. biometrics).
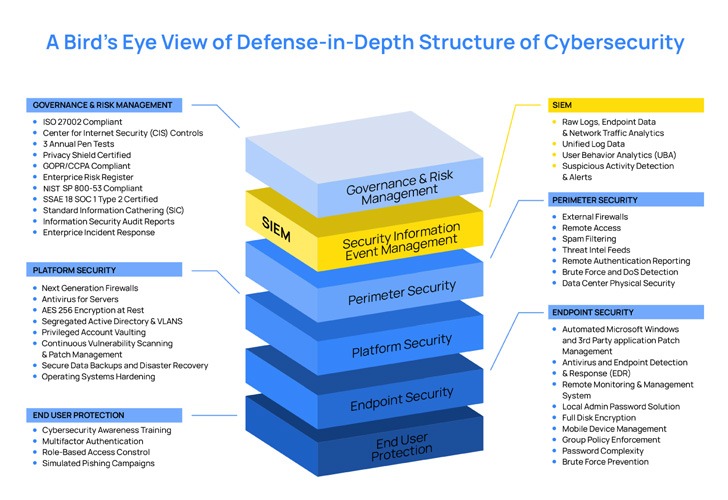
Network defense layers protection sequentially:
- Firewalls filter traffic at the perimeter
- Intrusion Detection Systems (IDS) monitor for threats behind the firewall, alerting without blocking
- Intrusion Prevention Systems (IPS) sit inline to actively block threats
- SIEM aggregates logs from all devices into centralized dashboards for real-time analysis and prioritization
Ongoing tasks include firewall rule audits, log analysis, patch management, and server backups. One-time configurations establish port filtering, role-based access, subnet segmentation, and encryption standards varying by data classification.
Cloud security follows the Shared Responsibility Model: providers secure physical infrastructure and hypervisors, while organizations must secure their data, applications, and service configurations.
Key techniques include server baseline images to detect unauthorized changes, cryptographic erasure (destroying encryption keys rather than data), and Hardware Security Modules (HSM) for secure key storage. Organizations often assume providers handle all security; correct configuration remains the customer’s responsibility.
Next
There was a lot more meat on this bone compared to the previous course. Next up are some fundamentals on Linux and SQL. Extremely basic stuff but we still need it for the Google’s Cybersecurity Professional Certificate.
