Introduction
I’m tackling the Google’s Cybersecurity Professional Certificate and I’ll share cliff notes on the courses I take. Dense summaries of what actually matters.
Today Assets, Threats, and Vulnerabilities of this Google security path.
Risk, assets and the CIA triad
Security starts with three non-negotiable pillars that we’ve covered before: confidentiality, integrity, and availability (the CIA triad). Everything else builds on protecting these qualities for your organization’s valuable assets.
- Risk is calculated as likelihood multiplied by impact; anything threatening the CIA triad of an asset
- Assets include data, devices, intellectual property, and people, classified by sensitivity
- Public
- Internal only
- Confidential
- Restricted
- The risk equation involves three elements: assets (what you protect), threats (why they are targeted), and vulnerabilities (how they are exploited)
- Data exists in three states requiring protection: in use (being accessed), in transit (traveling across networks), and at rest (in storage)
- Cloud security demands special attention to misconfiguration, which remain the leading cause of breaches
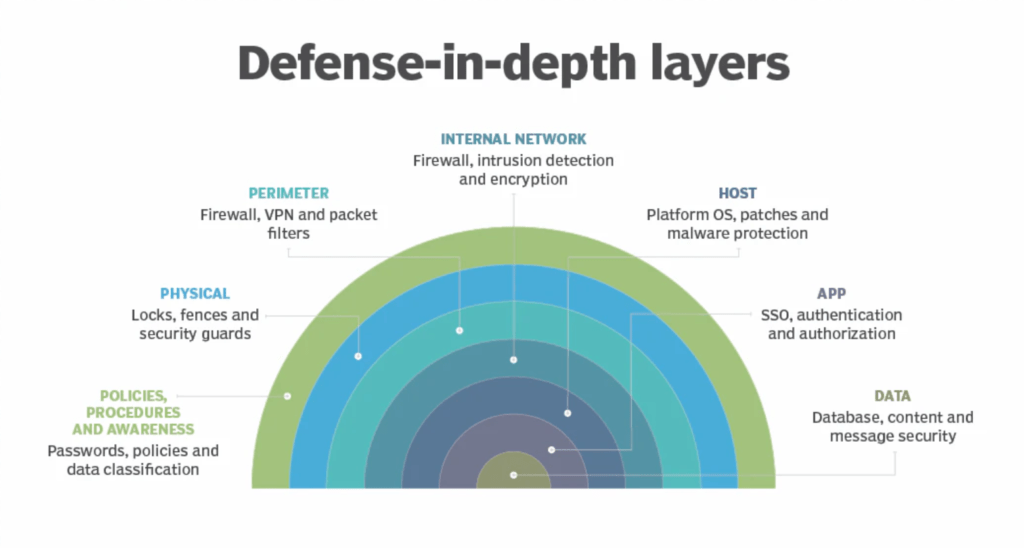
Building depth into security
No single control stops every threat. Defense in depth uses multiple overlapping safeguards across five layers (some models use less, some use more), ensuring that breaching one layer does not compromise the entire system.
- Perimeter layer filters external access through authentication like passwords and MFA
- Network layer controls traffic flow using firewalls and segmentation
- Endpoint layer protects individual devices with anti-malware and hardening
- Application layer secures software interfaces through secure coding and input validation
- Data layer encrypts and classifies sensitive information using the principle of least privilege
Controls fall into three categories
- Technical (encryption, firewalls)
- Operational (training, incident response)
- Managerial (policies, risk assessments)
Identity, access and accountability
Controlling who accesses what (and tracking what they do) forms the backbone of modern security operations.
- The AAA framework governs access
- Authentication (proving identity)
- Authorization (granting permissions)
- Accounting (logging activities)
- Principle of Least Privilege grants users only the minimum access required for their specific tasks, reducing blast radius if credentials are compromised
- Separation of duties divides critical functions among multiple people to prevent single-point misuse
- Account types require different oversight: guest accounts for external users, standard accounts for staff, service accounts for applications, and privileged accounts requiring extra monitoring
- Regular audits identify privilege creep (accumulated excessive permissions) and unauthorized account changes
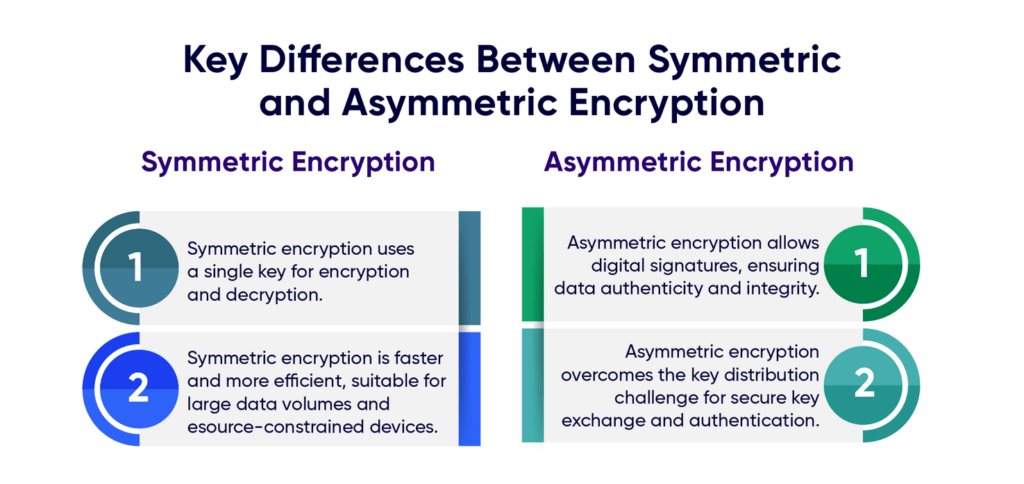
Cryptography, privacy and data protection
When controls fail, encryption and privacy practices provide the last line of defense for sensitive information.
- Symmetric encryption uses one secret key for fast data exchange; asymmetric encryption uses public-private key pairs for secure initial connections
- Hashing creates unique, irreversible digital fingerprints for verifying file integrity and storing passwords; always combined with salting to prevent rainbow table attacks
- Public Key Infrastructure (PKI) establishes trust through digital certificates issued by Certificate Authorities
- Legally protected data types include PII (personally identifiable information), PHI (health information under HIPAA), and SPII (sensitive PII requiring need-to-know access)
- Major compliance frameworks include GDPR (EU data rights), PCI DSS (payment card security), and HIPAA (US healthcare data)
The threat landscape
Understanding who attacks and how helps organizations anticipate rather than merely react to security incidents.
- Threat actors range from competitors and criminal syndicates to state actors and malicious insiders
- Advanced Persistent Threats (APTs) maintain long-term unauthorized access for espionage, often targeting supply chains to reach larger entities
- Social engineering exploits human psychology through pretexting, baiting, phishing, and tailgating, often bypassing technical controls entirely
- Malware categories include viruses (user-activated), worms (self-spreading), Trojans (disguised as legitimate software), ransomware (data encryption for extortion), and fileless malware (memory-resident threats)
- Webbased attacks like cross-site scripting (XSS), SQL injection, and cross-site request forgery (CSRF) exploit application coding flaws to steal sessions or manipulate databases
Vulnerability management and assessment
Proactive discovery and remediation of weaknesses before exploitation separates resilient organizations from vulnerable ones.
- Continuous four-step cycle
- Identify vulnerabilities
- Evaluate exploits
- Prepare defenses
- Assess effectiveness
- Vulnerability scanning compares systems against threat databases like the CVE (Common Vulnerabilities and Exposures) list, scored by CVSS (0-10 scale, where 9+ is critical)
- Penetration testing simulates real attacks through red team (offensive), blue team (defensive), or purple team (collaborative) exercises
- Open Source Intelligence (OSINT) gathers publicly available information to predict threats using tools like VirusTotal, MITRE ATT&CK, and Have I Been Pwned
- Patch management strategies must address end-of-life software risks and balance automatic updates (consistent but potentially unstable) against manual deployment (controlled but often delayed)
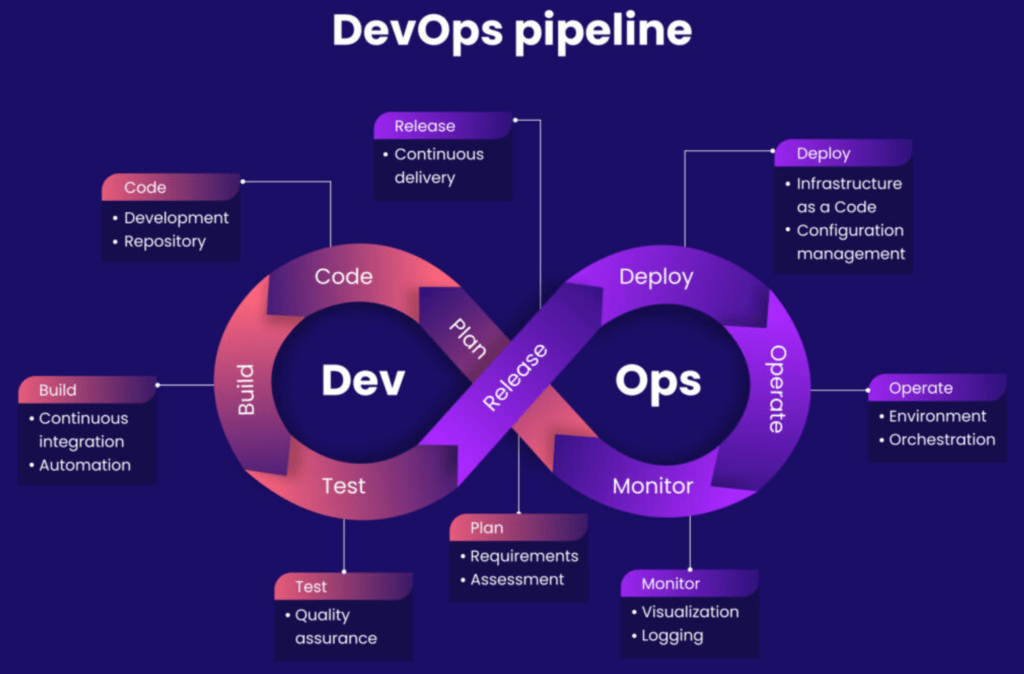
Secure development and threat modeling
Security integrated into the development lifecycle prevents vulnerabilities from reaching production environments.
- CI/CD pipelines require DevSecOps practices: automated security testing (SAST/DAST), dependency scanning, secrets management, and hardened build environments
- The OWASP Top 10 identifies critical web risks including broken access control, injection attacks, cryptographic failures, and insecure design
- Threat modeling systematically identifies threats through frameworks like STRIDE (spoofing, tampering, repudiation, information disclosure, denial of service, elevation of privilege) and PASTA (seven-stage risk-centric analysis)
- Key threat modeling questions:
- What are we building?
- What can go wrong?
- What are we doing about it?
Governance, compliance and risk management
Effective security requires documented processes, measured maturity, and continuous improvement.
- Security plans consist of policies (rules), standards (reference points), and procedures (step-by-step instructions)
- The NIST Cybersecurity Framework provides voluntary guidance across six functions (measured across four maturity tiers)
- Govern
- Identify
- Protect
- Detect
- Respond
- Recover
- Risk registers centralize potential threats with likelihood and severity scores to prioritize remediation efforts
- Compliance differs from frameworks: regulations are mandatory legal requirements, while frameworks are voluntary resources for improvement
- Security is ultimately a culture: a shared set of values spanning every organizational level, not merely a technical function
Next
This one had a lot of cool security information! I hope I was able to still make it a bit packed and concise, of course. Next course sounds promising: Sound the Alarm: Detection and Response.
